It’s come to our attention here at Backblaze that there’s a movie coming out later this week that some of you are excited about. A few of us around the office might be looking forward to it, too, and it just so happens that we have some special insight into key plot elements.
For instance, did you know that George Lucas was actually a data backup and cloud storage enthusiast? It’s true, and once you start to look, you can see it everywhere in the Star Wars storyline. If you aren’t yet aware of this deeper narrative thread, we’d encourage you to consider the following lessons to ensure you don’t suffer the same disruptions that Darth Sidious (AKA the Emperor, AKA Sheev Palpatine) and the Skywalkers have struggled with over the past 60 years of their adventures.
Because, whether you run a small business, an enterprise, the First Order, or the Rebel Alliance, your data—how you work with it, secure it, and back it up—can be the difference between galactic domination and having your precious battle station scattered into a million pieces across the cold, dark void of space.
Spoiler Alert: If you haven’t seen any of the movies we’ll reference below, well, you’ve got some work to do: about 22 hours and 30 minutes of movies, somewhere around 75 hours of animated and live action series, a few video games, and more novels than we can list here (don’t even start with the Canon and Legends division)… If you’d like to try, however, now is the time to close this tab.
Though we all know the old adage about “trying”…
Security:
Any good backup strategy begins with a solid approach to data security. If you have that in place, you significantly lower your chance of ever having to rely on your backups. Unfortunately, the simplest forms of security were often overlooked during the first eight installments of the Star Wars story…
“Lost a planet, Master Obi-Wan has. How embarrassing!”
–Master Yoda
The history of the Jedi Council is rife with infosec issues, but possibly the most egregious is called out when Obi-Wan looks into the origins of a Kamino Saberdart. Looking for the location of the planet Kamino itself within the Jedi Archives, he finds nothing but empty space. Having evidently failed out of physics at the Jedi Academy, Master Kenobi needs Yoda to point out that, if there’s a gravity well suggesting the presence of a planet—the planet has likely been improperly deleted from the archives. And indeed that seems to have been the case.
How does the galactic peacekeeping force stand a chance against the Sith when they can’t even keep their own library safe?
Some might argue that, since the Force is required to manipulate the Jedi Archives, then Jedi training was a certain type of password protection. But there were thousands of trained Jedi in the galaxy at that time, not to mention the fact that their sworn enemies were force users. This would be like Google and Amazon corporate offices sharing the same keycards—not exactly secure! So, at their most powerful, the Jedi had weak password protection with no permissions management. And what happened to them? Well, as we now know, even the Younglings didn’t make it… That’s on the Jedi Archivists, who evidently thought they were too good for IT.

“Most unfortunate about the security breach on Jedha, Director Krennic.”
—Grand Moff Tarkin
Of course, while the Jedi may have stumbled, the Empire certainly didn’t seem to learn from their mistakes. At first glance, the Imperial databank on Scarif was head-and-shoulders above the Jedi Archives. As we’ve noted before, that Shield Gate was one heck of a firewall! But Jyn Urso and Cassian Andor exploited a consistent issue in the Empire’s systems: Imperial Clearance Codes. I mean, did anyone in the galaxy not have a set of Clearance Codes on hand? It seems like every rebel ship had a few lying around. If only they had better password management, all of those contractors working on Death Star II might still be pulling in a solid paycheck.
To avoid bad actors poking around your archives or databanks, you should conduct regular reviews of your data security strategies to make sure you’re not leaving any glaring holes open for someone else to take advantage of. Regularly change passwords. Use two factor authentication. Use encryption. Here’s more on how we use encryption, and a little advice about ransomware.
3-2-1 Backup
But of course, we’ve seen that data security can fail, in huge ways. By our count, insufficient security management on both sides of this conflict has led to the destruction of 6 planets, the pretty brutal maiming of 2 others, a couple stars being sucked dry (which surely led to other planets’ destruction), and the obliteration of a handful of super weapons. There is a right way folks, and what we’re learning here is, they didn’t know it a long time ago in a galaxy far, far away. But even when your security is set up perfectly, disaster can strike. That’s why backups are an essential accompaniment to any security.
The best approach is a 3-2-1 backup strategy: For every piece of data, you have the data itself (typically on your computer), a backup copy on site (in a NAS or simply an external hard drive), and you keep one copy in the cloud. It’s the most reasonable approach for most average use cases. Lets see how the Empire managed their use case, when the stakes (the fate of much of existence) couldn’t have been higher:

“I will take the designs with me to Coruscant. They will be much safer there with my master.”—Count Dooku
We first see the plans for the “super weapon based on Geonosian designs” when Count Dooku, before departing Geonosis, decides that they would be safer housed on Coruscant with Darth Sidious. How wrong he was! He was thinking about securing his files, but it seems he stumbled en route to actually doing so.
By the time Jynn Erso learns of the “Stardust” version of the plans for the Death Star, it seems that Scarif is the only place in the Galaxy, other than on the Death Star itself, presumably, that a person could find a copy of the plans… Seriously? Technically, the copy on Scarif functioned as the Empire’s “copy in the cloud,” but it’s not like the Death Star had an external hard drive trailing it through space with another copy of the plans.
If you only have one backup, it’s better than nothing—but not by much. When your use case involves even a remote chance that Grand Moff Tarkin might use your data center for target practice, you probably need to be extra careful about redundancy in your approach. If the Rebel Alliance, or just extremely competitive corporate leaders, are a potential threat to your business, definitely ensure that you follow 3-2-1, but also consider a multi-cloud approach with backups distributed in different geographic regions. (For the Empire, we’d recommend different planets…)
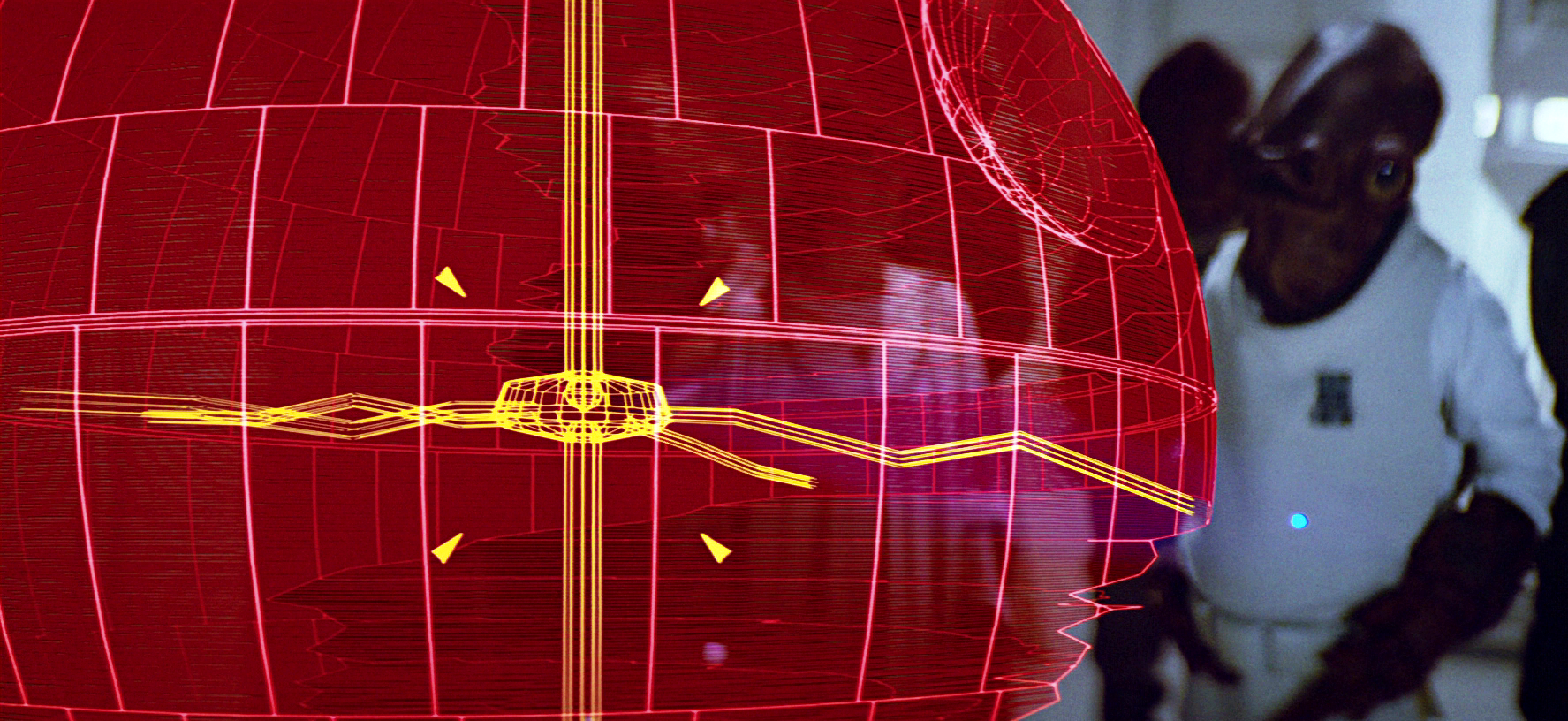
Version Control
There’s being backed up, and then there’s being sure you have the right thing backed up. One thing we learn from the plans used to defeat the first Death Star is that the Empire didn’t manage version control very well. Take a close look at the Death Star schematic that Jyn and Cassian absconded with. Notice anything…off?
Yeah, that’s right. The focus lens for the superlaser is equatorial. Now, everyone knows that the Death Star’s superlaser is actually on the northern hemisphere. Which goes to show you that this backup was not even up to date! A good backup solution will run on a daily basis, or even more frequently depending on use cases. It’s clear that whatever backup strategy the Death Star team had, it had gone awry some time ago.
“The rebels managed to destroy the first Death Star. By rebuilding the Death Star, and using it as many times as necessary to restore order, we prove that their luck only goes so far. We prove that we are the only galactic authority and always will be.”―Lieutenant Nash Windrider
We can only imagine that the architects who were tasked with quickly recreating the Death Star immediately contacted the Records Department to obtain the most recent version of the original plans. Imagine their surprise when they learned that Tarkin had destroyed the databank and they needed to work from memory. Given the Empire’s legendarily bad personnel management strategies—force-choking is a rough approach to motivation, after all—it’s easy to assume that there were corners cut to get the job done on the Emperor’s schedule.
Of course, it’s not always the case that the most recent version of a file will be the most useful. This is where Version History comes into the picture. Version History allows users to maintain multiple versions of a file over extended periods of time (including forever). If the design team from the Empire had set up Version History before bringing Galen Erso back on board, they could have reverted to the pre-final plans that didn’t have a “Insert Proton Torpedo Here To Destroy” sign on them.
To their credit, the Death Star II designers did avoid the two-meter-wide thermal exhaust port exploited by Luke Skywalker at the Battle of Yavin. Instead, they incorporated millions of millimeter-sized heat-dispersion tubes. Great idea! And yet, someone seemed to think it was okay to incorporate Millenium Falcon-sized access tunnels to their shockingly fragile reactor core? This shocking oversight seems to be either a sign of an architectural team clearly stressed by the lack of reliable planning materials, or possibly it was their quiet protest at the number of their coworkers who Darth Vader tossed around during one of his emotional outbursts.
Cloud Storage Among the Power (Force) Users
At this point it is more than clear that the rank-and-file of pretty much every major power during this era of galactic strife was terrible at data security and backup. What about the authorities, though? How do they rank? And how does their approach to backup potentially affect what we’ll learn about the future of the Galaxy in the concluding chapter of the Star Wars saga, “The Rise of Skywalker”?
There are plenty of moderately talented Jedi out there, but only a few with the kind of power marshaled by Yoda, Obi-Wan, and Luke. Just so, there are some of us for whom computer backup is about the deepest we’ll ever dive into the technology that Backblaze offers. For the more ambitious, however, there’s B2 Cloud Storage. Bear with us here, but, is it possible that these Master Jedis could be similar to the sysadmins and developers who so masterfully manipulate B2 to create archives, backup, compute projects, and more, in the cloud? Have the Master Jedis manipulated the force in a similar way to use it as a sort of cloud storage for their consciousness?

“If you strike me down, I shall become more powerful than you can possibly imagine.”—Obi-Wan Kenobi
Over many years, we’ve watched as force ghosts accumulate on the sidelines: First Obi-Wan, then Yoda, Anakin Skywalker, and, presumably, Luke Skywalker himself at the end of “The Last Jedi.” (Even Qui-Gon Jinn evidently figured it out after some post-mortem education.) If our base level theory that Star Wars is actually an extended metaphor for the importance of a good backup strategy, then who better to redeem the atrocious backup track record so far than the strongest Jedi the galaxy has ever known? In backing themselves up to the cloud, does “Team Force Ghost” actually present a viable recovery strategy from Darth Sidious’ unbalancing of the force? If so, we could be witnessing one of the greatest arguments for cloud storage and computing ever imagined!
“Long have I waited…”—Darth Sidious
Of course, there’s a flip-side to this argument. If our favorite Jedi Masters were expert practitioners of cloud storage solutions, then how the heck did someone as evil as Darth Sidious find himself alive after falling to his death in the second Death Star’s reactor core? Well, there is precedent for Sith Masters’ improbable survival after falling down lengthy access shafts. Darth Maul survived being tossed down a well and being cut in half by Obi-Wan when Darth Vader was just a glimmer in Anakin Skywalker’s eye. But that was clearly a case of conveniently cauterized wounds and some amazing triage work. No, given the Imperial Fleet’s response to Darth Sidious’ death, the man was not alive at the end of the Battle of Endor by any conventional definition.
One thing we do know, thanks to Qui-Gon’s conversations with Yoda after his death, is that Dark Siders can’t become force ghosts. In short, to make the transition, one has to give in to the will of the Force—something that practitioners of the Dark Side just can’t abide.
Most theories point to the idea that the Sith can bind themselves to objects or even people during death as a means of lingering among the living. And of course there is the scene in “Revenge of the Sith” wherein Darth Sidious (disguised as Sheev Palpatine) explains how Darth Plagueis the Wise learned to cheat death. How, exactly, this was achieved is unclear, but it’s possible that his method was similar to other Sith. This is why, many speculate, we see our intrepid heroes gathering at the wreckage of the second Death Star: Because Darth Sidious’ body is tied, somehow, to the wreckage. Classic! Leave it up to old Sidious to count on a simple physical backup, in the belief that he can’t trust the cloud…

You Are One With The Force, And The Force Is With You
Are we certain how the final battle of the Star Wars story will shape up? Will Light Side force wielders using Cloud Storage to restore their former power, aid Rey and the rest of our intrepid heroes, and defeat the Sith, who have foolishly relied on on-prem storage? No, we’re not, but from our perspective it seems likely that, when the torch was passed, George Lucas sat J.J. Abrams down and said, “J.J., let me tell you what Star Wars is really all about… data storage.”
We are certain, however, that data security and backup doesn’t need to be a battle. Develop a strategy that works for you, make sure your data is safe and sound, and check it once in awhile to make sure it’s up to date and complete. That way, just like the Force, your data will be with you, always.