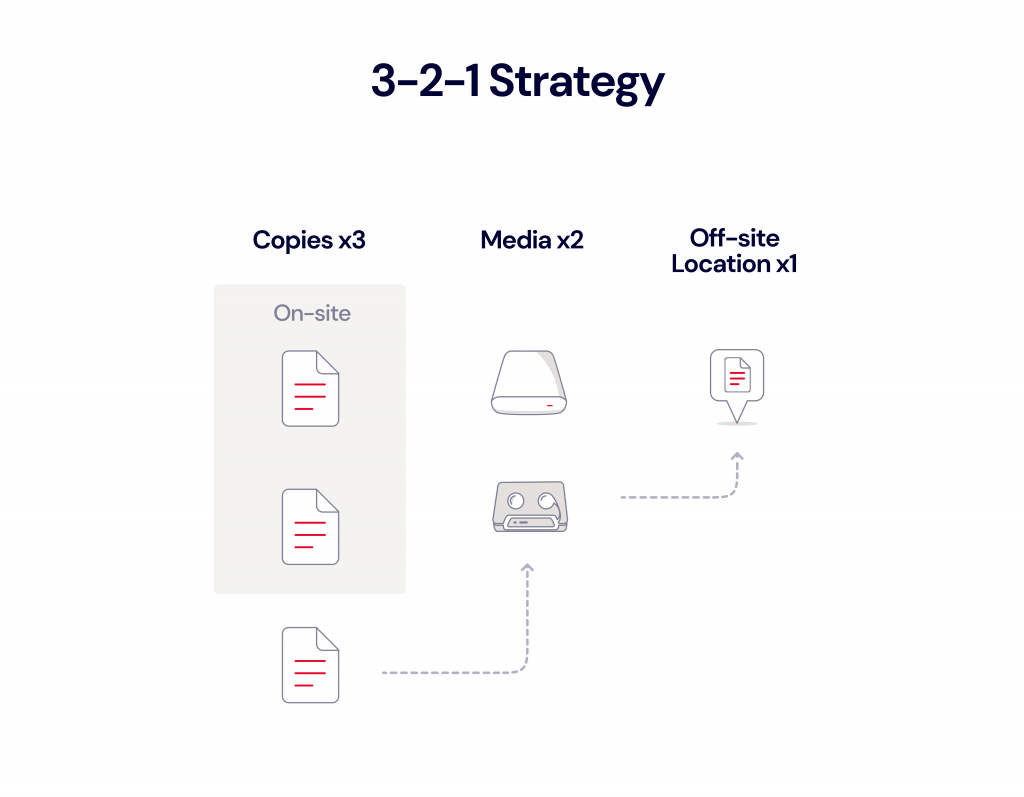
When it comes to having a backup plan, Navy SEALs go by the rule that “Two is one and one is none.” They’re not often one-upped, but in the world of computer backup, even two is none. The gold standard until recently has been the 3-2-1 rule—three copies of your data on two different media with one copy stored off-site.
The 3-2-1 rule still has value, especially for individuals who aren’t backing up at all. But today, the gold standard is evolving. In this post, we’ll explain why 3-2-1 is being replaced by more comprehensive strategies; we’ll look at the difference between the 3-2-1 rule and emerging rules, including 3-2-1-1-0 and 4-3-2; and we’ll help you decide which is best for you.
Implementing Advanced Backup Strategies With Backblaze Cloud Replication
Backblaze Cloud Replication is a new service that allows customers to automatically store and sync data in different locations—across regions, across accounts, or in different buckets within the same account. There are three main reasons you might want to use Backblaze Cloud Replication:
- Data Redundancy: Replicating data for security, compliance, and continuity purposes.
- Data Proximity: Bringing data closer to distant teams or customers for faster access.
- Replication Between Environments: Replicating data between testing, staging, and production environments when developing applications.
Click here to learn more and get started today if you’re not yet a Backblaze B2 customer.
Why Is the 3-2-1 Backup Strategy Falling Out of Favor?
When the 3-2-1 backup strategy gained prominence, the world looked a lot different than it does today, technology-wise. The rule is thought to have originated in the world of photography in Peter Krogh’s 2009 book, “The DAM Book: Digital Asset Management for Photographers.” At that time, tape backups were still widely used, especially at the enterprise level, due to their low cost, capacity, and longevity.
The 3-2-1 strategy improved upon existing practices of making one copy of your data on tape and keeping it off-site. It advised keeping three copies of your data (e.g., one primary copy and two backups) on two different media (e.g., the primary copy on an internal hard disk, a backup copy on tape, and an additional backup copy on an external HDD or tape) with one copy off-site (likely the tape backup).
Before cloud storage was widely available, getting the third copy off-site usually involved hiring a storage service to pick up and store the tape drives or physically driving them to an off-site location. (One of our co-founders used to mail a copy of his backup to his brother.) This meant off-site tape backups were “air-gapped” or physically separated from the network that stored the primary copy by a literal gap of air. In the event the primary copy or on-site backup became corrupted or compromised, the off-site backup could be used for a restore.
As storage technology has evolved, the 3-2-1 backup strategy has gotten a little…cloudy. A company might employ a NAS device or SAN to store backups on-site, which is then backed up to object storage in the cloud. An individual might employ a 3-2-1 strategy by backing up their computer to an external hard drive as well as the cloud.
While a 3-2-1 strategy with off-site copies stored in the cloud works well for events like a natural disaster or accidental deletion, it lost the air gap protection that tape provided. Cloud backups are sometimes connected to production networks and thus vulnerable to a digital attack.
Ransomware: The Driver for Stronger Backup Strategies
With as many high-profile ransomware incidents as the past few months have seen, it shouldn’t be news to anyone that ransomware is on the rise. Ransom demands hit an all-time high of $50 million in 2021 so far, and attacks like the ones on Colonial Pipeline and JBS Foods threatened gas and food supply chains. In their 2021 report, “Detect, Protect, Recover: How Modern Backup Applications Can Protect You From Ransomware,” Gartner predicted that at least 75% of IT organizations will face one or more attacks by 2025.
Backups are meant to be a company’s saving grace in the event of a ransomware attack, but they only work if they’re not compromised. And hackers know this. Ransomware operators like Sodinokibi, the outfit responsible for attacks on JBS Foods, Acer, and Quanta, are now going after backups in addition to production data.
Cloud backups are sometimes tied to a company’s active directory, and they’re often not virtually isolated from a company’s production network. Once hackers compromise a machine connected to the network, they spread laterally through the network attempting to gain access to admin credentials using tools like keyloggers, phishing attacks, or by reading documentation stored on servers. If a hacker has Active Directory admin credentials all backups secured with that Active Directory are vulnerable.
Is a 3-2-1 Backup Strategy Still Viable?
As emerging technology has changed the way backup strategies are implemented, the core principles of a 3-2-1 backup strategy still hold up:
- You should have multiple copies of your data.
- Copies should be geographically distanced.
- One or more copies should be readily accessible for quick recoveries in the event of a physical disaster or accidental deletion.
But, they need to account for an additional layer of protection: One or more copies should be physically or virtually isolated in the event of a digital disaster like ransomware that targets all of their data, including backups.
What Backup Strategies Are Replacing 3-2-1?
A 3-2-1 backup strategy is still viable, but more extensive, comprehensive strategies exist that make up for the vulnerabilities introduced by connectivity. While not as catchy as 3-2-1, strategies like 3-2-1-1-0 and 4-3-2 offer more protection in the era of cloud backups and ransomware.
What Is 3-2-1-1-0?
A 3-2-1-1-0 strategy stipulates that you:
- Maintain at least three copies of business data.
- Store data on at least two different types of storage media.
- Keep one copy of the backups in an off-site location.
- Keep one copy of the media offline or air gapped.
- Ensure all recoverability solutions have zero errors.
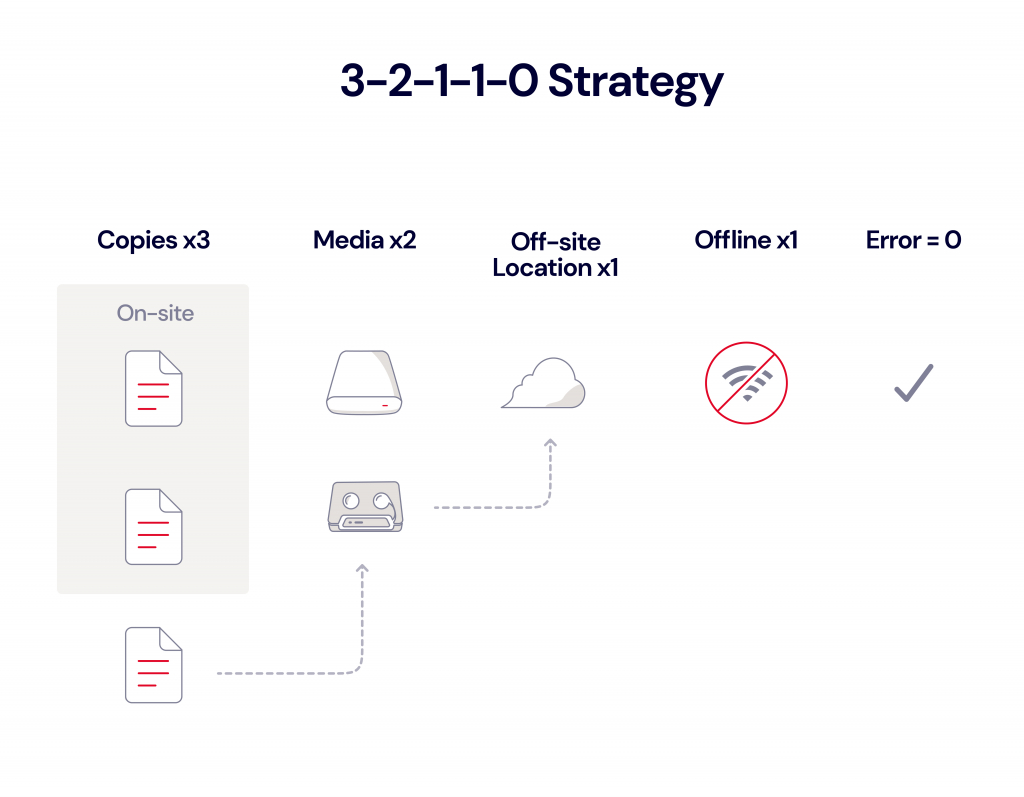
The 3-2-1-1-0 method reintroduced the idea of an offline or air gapped copy—either tape backups stored off-site as originally intended in 3-2-1, or cloud backups stored with immutability, meaning the data cannot be modified or changed.
If your company uses a backup software provider like Veeam, storing cloud backups with immutability can be accomplished by using Object Lock. Object Lock is a powerful backup protection tool that prevents a file from being altered or deleted until a given date. Only a few storage platforms currently offer the feature, but if your provider is one of them, you can enable Object Lock and specify the length of time an object should be locked in the storage provider’s user interface or by using API calls.
When Object Lock is set on data, any attempts to manipulate, encrypt, change, or delete the file will fail during that time. The files may be accessed, but no one can change them, including the file owner or whoever set the Object Lock and—most importantly—any hacker that happens upon the credentials of that person.
The 3-2-1-1-0 strategy goes a step further to require that backups are stored with zero errors. This includes data monitoring on a daily basis, correcting for any errors as soon as they’re identified, and regularly performing restore tests.
A strategy like 3-2-1-1-0 offers the protection of air gapped backups with the added fidelity of more rigorous monitoring and testing.
What Is 4-3-2?
If your data is being managed by a disaster recovery expert like Continuity Centers, for example, your backups may be subscribing to the 4-3-2 rule:
- Four copies of your data.
- Data in three locations (on-prem with you, on-prem with an MSP like Continuity Centers, and stored with a cloud provider).
- Two locations for your data are off-site.
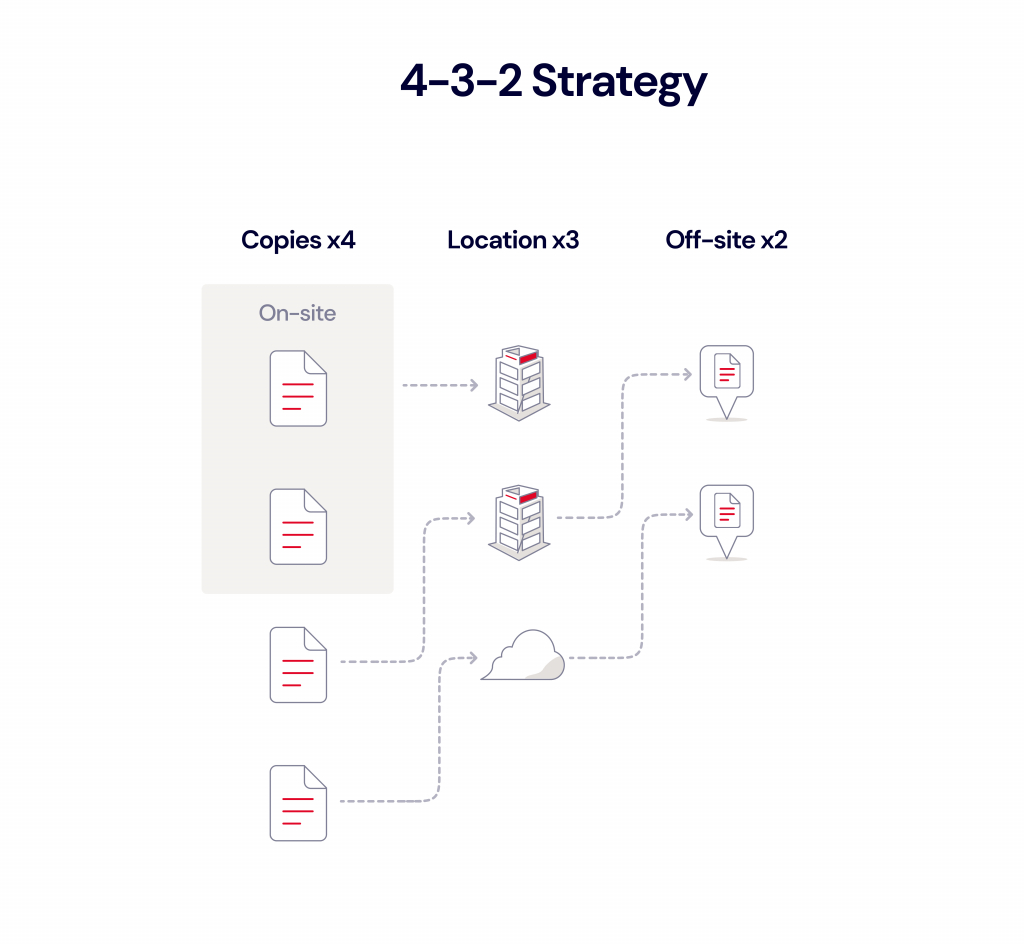
Continuity Centers’ CEO, Greg Tellone, explained the benefits of this strategy in a session with Backblaze’s VP of Sales, Nilay Patel, at VeeamON 2021, Veeam’s annual conference. A 4-3-2 strategy means backups are duplicated and geographically distant to offer protection from events like natural disasters. Backups are also stored on two separate networks, isolating them from production networks in the event they’re compromised. Finally, backup copies are stored with immutability, protecting them from deletion or encryption should a hacker gain access to systems.
Warning
Some cloud service providers suggest that backup strategies employing multiple vendors reflect those vendors’ unreliability for data storage, but redundant failsafes should always be part of your plan. The truth is that anything and everything can fail. Hard drives fail. Good employees make bad mistakes. Bad employees make worse mistakes. And, whether it was the Amazon Web Services outage that took down a large swath of the internet or the Google Cloud Storage outage that affected platforms like Snapchat, Shopify, and Discord, even the biggest providers can let you down in your time of need. Smart business people work from that assumption regardless of their chosen provider.
Which Backup Strategy Is Right for You?
First, any backup strategy is better than no backup strategy. As long as it meets the core principles of 3-2-1 backup, you can still get your data back in the event of a natural disaster, a lost laptop, or an accidental deletion. To summarize, that means:
- Keeping multiple copies of your data—at least three.
- Storing copies of your data in geographically separate locations.
- Keeping at least one copy on-site for quick recoveries.
With tools like Object Lock, you can apply the principles of 3-2-1-1-0 or 4-3-2, giving your data an additional layer of protection by virtually isolating it so it can’t be deleted or encrypted for a specific time. In the unfortunate event that you are attacked by ransomware, backups protected with Object Lock allow you to recover.
For more information on how you can protect your company from ransomware, check out our guide to recovering from and preventing a ransomware attack.