Today, we are pleased to announce two new security features for Backblaze. Security is a top priority at Backblaze, and we are fully committed to, and proactively invest in, keeping our users secure.
In 2015, we added additional features such as two-factor verification via SMS, which enables customers to use a mobile device to verify their identity when accessing their accounts. Earlier this year we added the ability to use mobile authenticator applications such as Google Authenticator and Authy, providing an additional method for two-factor verification. Authenticator apps provide convenience and an additional layer of access security to accounts should the user have internet access but not cell phone carrier access.
Why Enable Two-Factor for Your Backblaze Account?
We have built our cloud backup and storage products with best-in-class security. As you may know, however, users sometimes unknowingly use practices that provide a point of access they didn’t intend — such as using the same credentials for more than one account or website. By enabling two-factor, you create a level of protection for your account that is much harder to penetrate, even for someone who has somehow obtained your credentials. It’s a smart precaution and should be used on every account where the option is available.
We are the only backup company that provides this level to security to all our customers, no matter what type of account they have. We strongly encourage all our users to use two-factor authentication for their Backblaze accounts.
What’s New?
This week we added two new features that further enhance Two-Factor Verification, Fallback to SMS and Backup Codes. These features are available to all our customers on all accounts, and make our already strong account security even better.
Two-Factor Fallback to SMS
Previously, users could select to have an SMS message sent to them to verify their identity whenever they signed into their account. Some users prefer the convenience and security of an authenticator app, but if they lose access to their phone, would be unable to verify their identity. For these users, we now add “Fallback to SMS,” which will enable the user to request an SMS message to verify their identity as an alternative to not having the authenticator app.
Two-Factor Backup Codes
What happens if you’ve chosen to use Two-Factor Verification using an authenticator app or SMS and you’ve lost access to your phone and the ability to receive an SMS (or don’t wish to use SMS)?
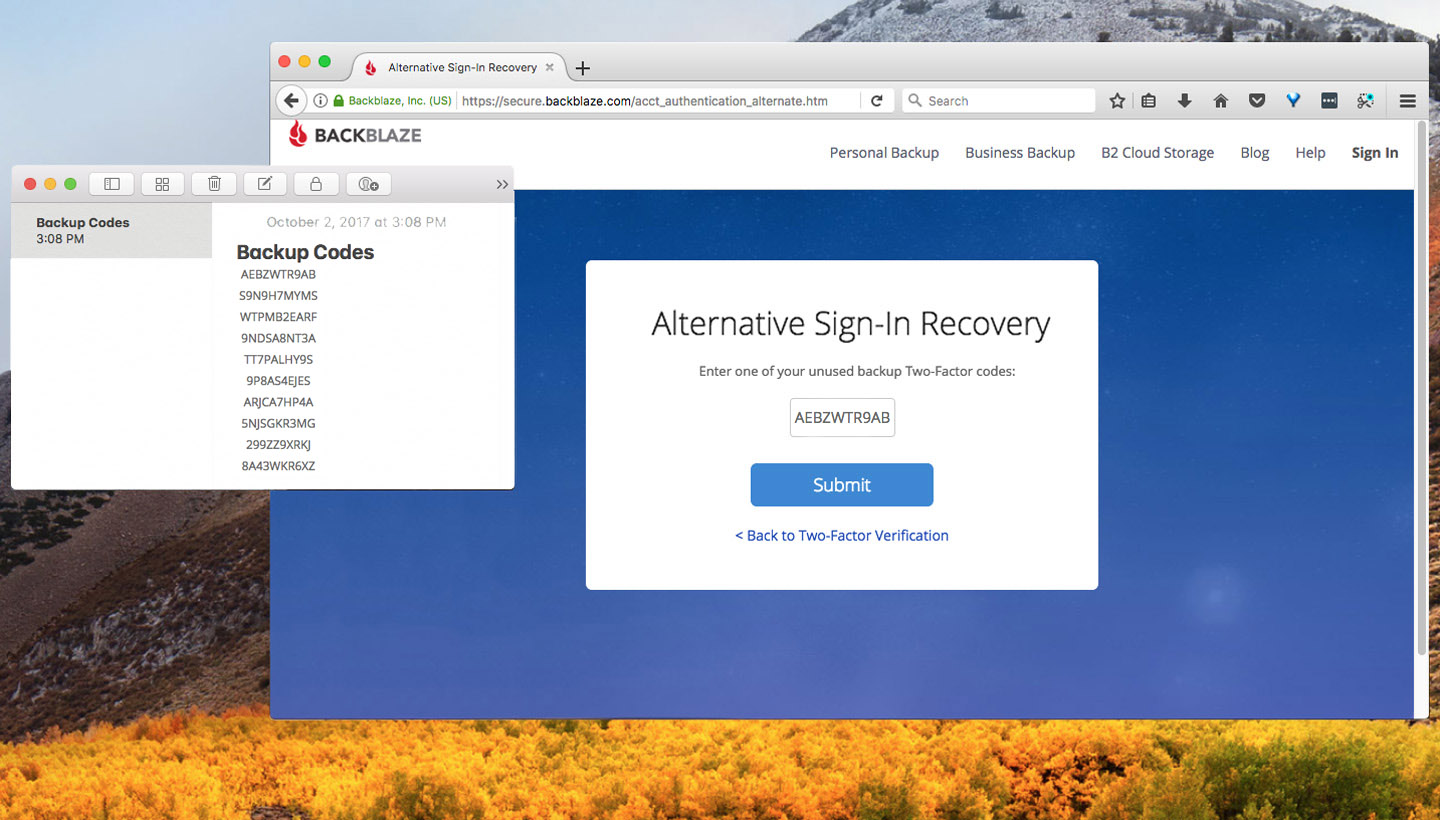
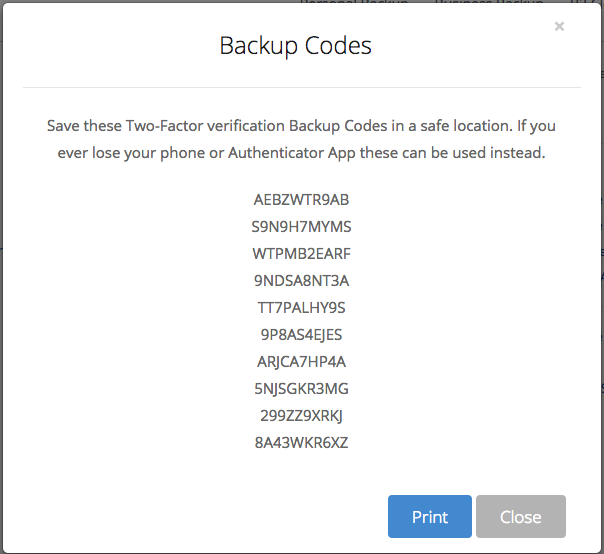
That’s where Backup Codes come in. By selecting “Get backup codes” on your account settings page, you will receive 10 codes that you can use to verify your identify when you sign into your account. You can copy these codes to a password manager, a notes program, or a file on your computer. Each of these codes can be used only once. If you use up all ten, or wish to revoke them, you can request a new set in your account settings.
Be aware that each of these backup codes gives someone with your credentials access to your account. We strongly recommend using a password manager or another secure location to keep these codes safe. When you select a new set of codes, your previous set will be invalidated, so be sure to replace the old backup codes you’ve saved with the new ones.
Here’s How It Works
Let’s say you’re trying to sign into your account and you’ve previously activated Two-Factor Verification with an authenticator app. For whatever reason, you don’t have access to your mobile device with the authenticator app.
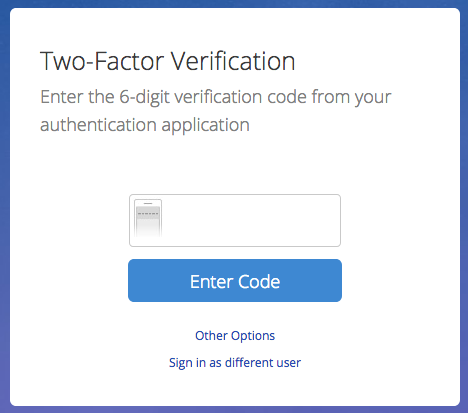
This is the dialog you would see after entering your email and password.
Without access to your authenticator app — and either Two-Factor Fallback to SMS or Backup Codes — you would be at a dead-end. You could not access your account.
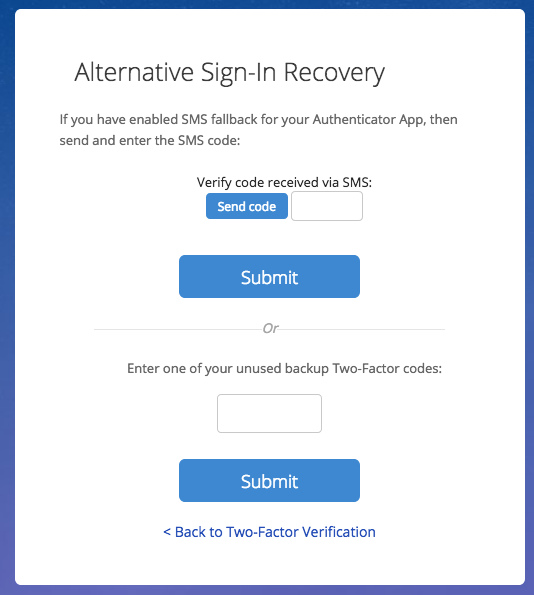
But, if you have these new options, Fallback to SMS and/or Backup Codes, activated in your account, you would be able to select “Other Options” at the bottom of the dialog. This is the dialog you would see.
You can now request that a code be sent to you via SMS (if you have that ability), or you could use one of your unused Backup Codes to sign into your account.
How to Enable These New Options
To enable one or both of these new options, sign into your Backblaze account. From the Overview page, select “My Settings” under Account.
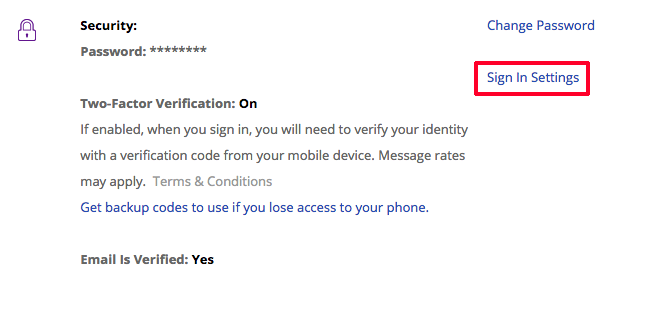
In the middle of the “My Settings” page, you will see the section entitled, Security. Select “Sign In Settings” on the right side.
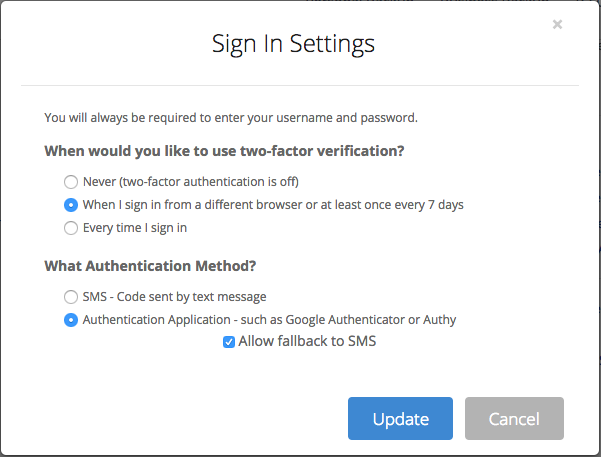
In the Sign In Settings dialog you can select your preferences for Two-Factor Verification. If you are using an authenticator app, we suggest you select “Allow fallback to SMS.”
Select Update and exit the dialog.
You are now back in the “My Settings” dialog. In the Security section, select Get backup codes to use if you lose access to your phone.
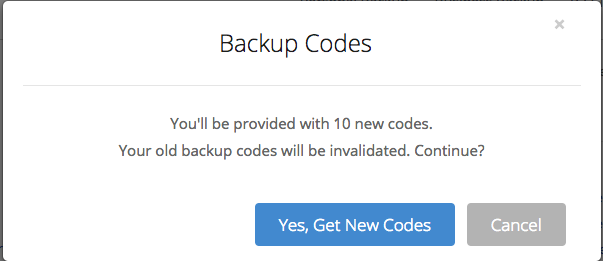
You will be asked if you wish to receive new backup codes. Select “Yes, Get New Codes.”
You will see a dialog containing 10 10-character alphanumeric codes. You should copy these codes to a safe place.
(No, these aren’t real codes — we knew you would ask.)
The ability to receive an SMS code or to use a backup code ensures that you will be able to verify your identify and sign into your account even if you don’t have your mobile device or access to a cell network.
Backup Codes Also Aid Estate and Emergency Planning
It’s a digital world now and we all need to plan for how our family and trusted others will access our online accounts and data if we are incapacitated or deceased. You can give your credentials and backup code(s) to someone you trust who might someday need access to your Backblaze account.
Some password manager applications, such as LastPass and 1Password, let you configure emergency access to your account credentials, account numbers, and other important information should that become necessary. This is a great place to store your Backblaze credentials and FallBack Backup Codes so they are available to your trusted contacts should that become necessary.
Backblaze Advises All Customers to Use Two Factor Verification with Fallback
If you haven’t already turned on Two-Factor Verification in the first place, go to the Sign-In Settings dialog in your Backblaze account and enable Two-Factor Verification.
After you’ve done that and you’ve also selected one or both fallback options described above, you’re all set.
Please let us know if you have any questions about these new security features or best practices for protecting your online accounts and digital assets.