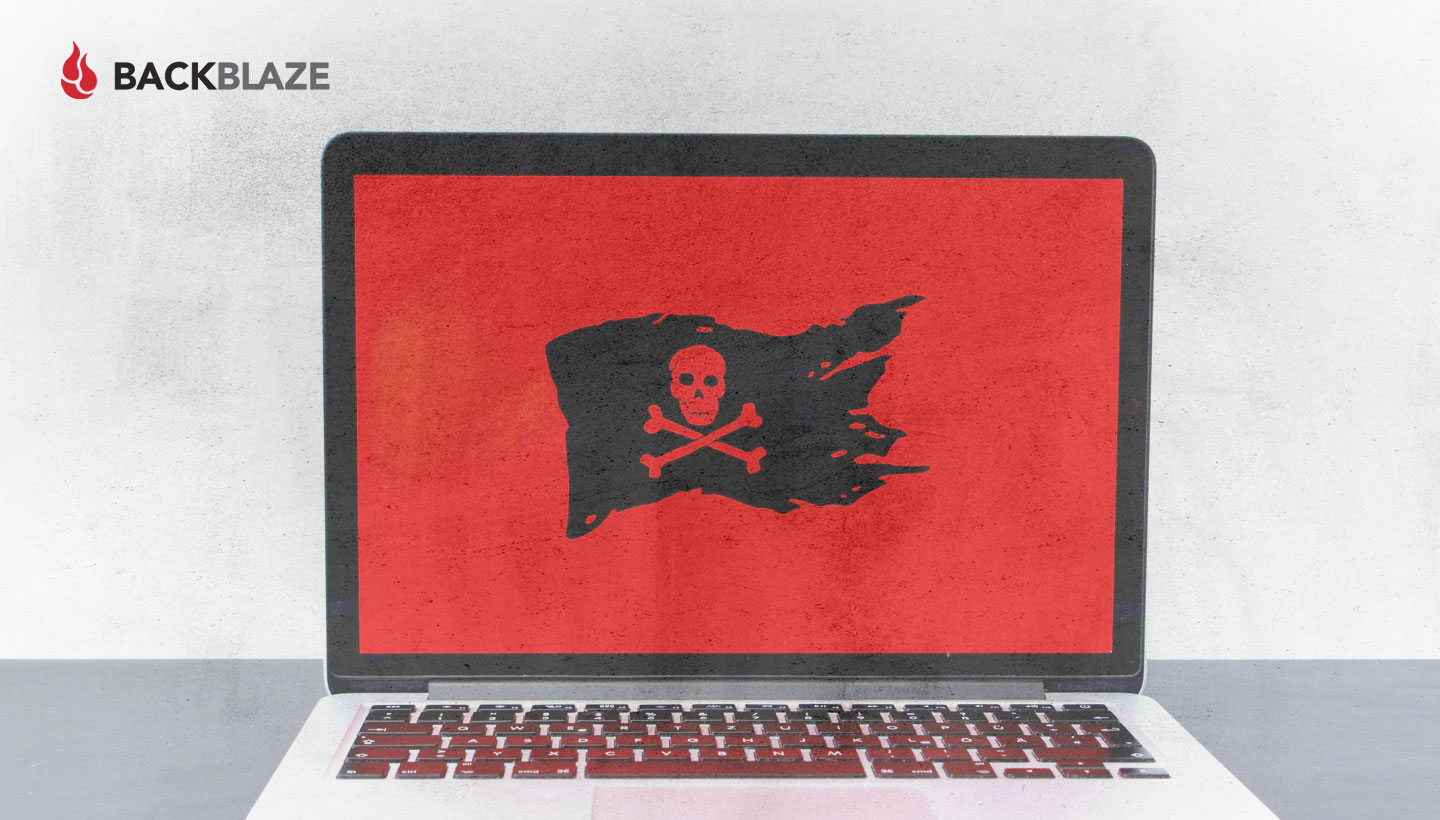
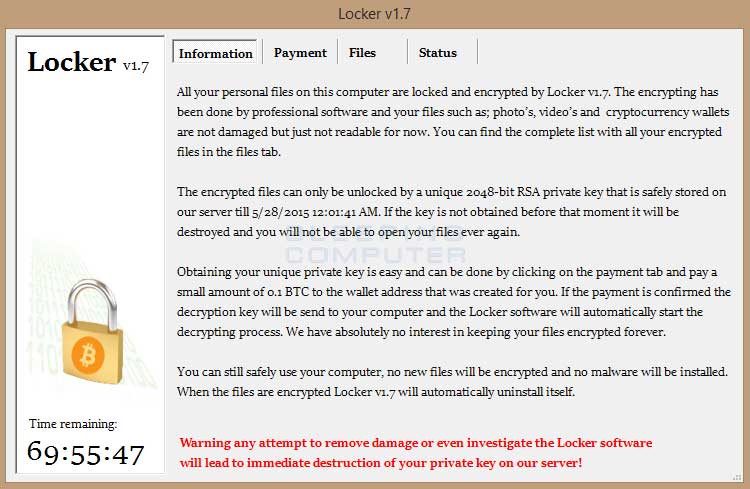
At midnight on May 25th, a dormant strain of ransomware awoke and began to wreak havoc on the systems and networks it had infected. The ransomware, known as Locker, was continuing in the footsteps of its ancestors, (Cryptolocker, CTB Locker, Cryptowall, and others) infecting systems, encrypting files, and then extorting money from people, businesses, and organizations to decrypt the affected files. For anyone who received the following message on May 25th, it was a very bad day.
A Very Brief History of Ransomware
The first known ransomware attack was in 1989 using the AIDS Trojan/PC Borg malware. An infected computer would display a message to the user that one of their programs had expired and they needed to pay $189 to have it restored. The creator was eventually caught and the ransomware genre went underground for several years, though it reappeared briefly in 2005 and 2006. It wasn’t until 2013 with the introduction of Cryptolocker and its subsequent variants and copycats, that ransomware became widely known.
The Locker Attack
Locker was unusual in that it was “sleeper” ransomware, having been dormant on the infected systems and devices until May 25th. The malware could have been installed anytime in the previous weeks, while it waited to be activated. For this reason it was difficult to pin down the attack vector, although a compromised Minecraft installer was suspected.
The “cost” to recover the files encrypted by Locker was 0.1 Bitcoins (about $24 USD), a modest amount when compared with previous ransomware attacks that demanded five to 10 times as much to recover the files they encrypted. On the bright side, according to security experts, nearly everyone who made the proper payment had their files decrypted.
Attack Vectors: How Do You Get Infected in the First Place?
There are several different ways for malware to get on a computer. For example, Java and Adobe-based vulnerabilities are often utilized to create exploits that can be used by ransomware builders. Anti-virus vendors are in a constant battle with these hackers, trying to stop the malware they create from being successfully downloaded and installed on your computer. This is a never-ending job, but there are ways you can help. One of the most common attack vectors is a phishing email. Here’s an example below that our CEO received.
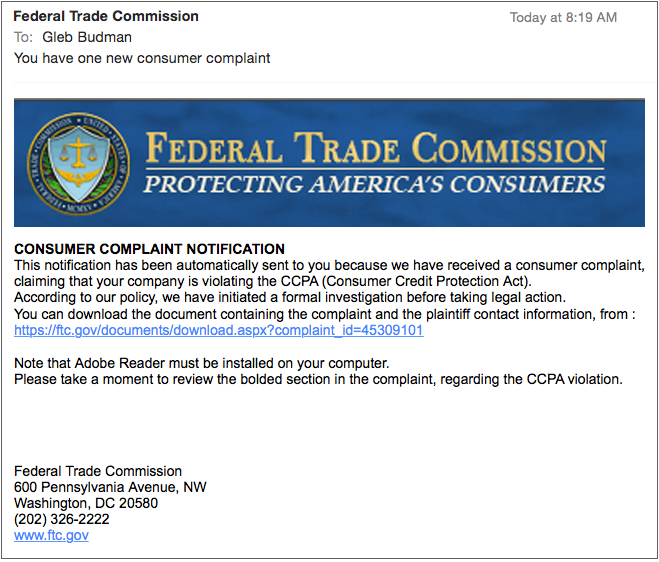
Phishing emails came to prominence in 2003 and have been a staple of attackers since then. A good attack will look just like an email you could receive, whether at your business or at home. The email above is likely to be what is known as spear phishing, meaning the attacker tailored the attack in some way towards the person or organization receiving the email. In this case, Gleb, as our CEO, would be a reasonable person to receive such a document, if it were real. It should be noted that the FTC does not send such emails, but I don’t think it’s possible for the average American to know exactly what the government doesn’t do! That is the social engineering paradox of phishing emails—you often don’t know what you don’t know.
Let’s look at the example of your password to an online account: your Bank, Amazon, iTunes, etc. What is the policy for how often you are required to change your password? If a change is required, how are you notified—email, perhaps? What happens if you forget your password? What information do you have to enter to change/recover your password? Can it be done online (very convenient) or will they send you an email? Now multiply these questions times the number of your online accounts that have a password. The answer equals the challenge you face in knowing whether an email from one of those online accounts is real or fake. Ignoring every email could mean losing access to a site you enjoy or need; clicking on every link is certain disaster.
Obviously we recognized this email as a phishing attack, but imagine what could happen if an intern or a new employee received such an email. Would they click the link just trying to be helpful? What about a curious employee? The thing we do know is that once the link is clicked, the malware’s wheels are set in motion.
As an example of how ransomware works, let’s take a look how Cryptolocker does its work.
- When the link is clicked, a Zbot variant is downloaded on the system and the Cryptolocker ransomware is installed.
- The malware is added to the system startup under a random name and then reaches out over the internet to establish communication with a command and control (C&C) server.
- Upon successful communication with the C&C system the server sends a public encryption key to encrypt the files. It also sends a corresponding Bitcoin address to accept payment.
- Using asymmetric encryption, the public key is used to encrypt 70 different types of files on the system. It will take the private key to decrypt the files. The private key resides with the C&C server.
- Once the files are encrypted, the user is presented with a screen similar to the image below, and the countdown begins. If the ransom is paid, the private key is sent to the infected system and the files are decrypted.

Options to Avoid Paying the Ransom
If there is nothing of value on your system, be it at home or at work, then the obvious thing to do is ignore the ransom message and have the system completely reinitialized. All your data will be gone, but you will still have your money.
Assuming that you have something of value on your computer, you could ignore the ransomware message and restore your data from a backup copy. You may have a personal local external drive or your organization may utilize a file server. In either case, you can recover your files from these sources. Trouble is, newer versions of ransomware, CTB Locker for example, are one step ahead of you. When installed and activated, this type of ransomware will not only encrypt the files on your computer, but it will also attempt to encrypt anything else connected to the computer, such as external hard drives and file servers. Such ransomware can reach out across the network to encrypt any files in nearly any location you have permission to store files. This includes the files stored in cloud-based directories and folders on your desktop by applications such as Dropbox. Sometimes, single sign-on is a bitch.
Best Practices to Keep from Getting Infected in the First Place
While there are no guarantees, here are some tips on how to keep your computer from getting infected with ransomware. You don’t have to do all of these, but the more you do, the better off you are.
- Keep your operating system up to date. This starts with knowing how your system is updated: automatically or manually by you.
- Know how your applications are updated. Some applications will pop up notifications on your screen, others will notify you via email and still others will only tell you about updates when you use them. If you get a notice you don’t expect, contact the company and ask.
- Keep your applications up to date. When new updates come out, especially security updates, apply them. But first, make sure you know how the application is updated (see item 2).
- If you receive a suspicious email (phishing?), but are not sure, contact the company by going to their website or contact them via phone. Don’t click on any links or use the phone numbers in the email.
- Use anti-virus software and keep it up to date. This should include a good adware filter and a pop-up blocker.
- Try not to click on ads for products or companies you don’t know. Even better, if you see an appealing ad, go directly to the company’s website and see if the offer is there.
- Only download and install browser add-ons, plugins, and extensions that come from known, reputable sources.
- Take a snapshot of your entire system from time to time, perhaps once a month. This will include data and applications. Store these snapshots on an external drive that is only connected to your computer to do the backup and then is disconnected.
- Have a backup of all the files on your computer to a server that is NOT on your network. Online backup systems such as Backblaze are good for this purpose as they utilize their own application to manage the transfer and storage of your data files.
- Awareness is key. As a computer user, your job is to stay aware of what’s happening on your computer. You don’t have to be a computer security expert, but you should practice safe clicking. Even the safest computer users can get infected with malware, but by staying alert and aware, you can dramatically reduce your chances.
The Future of Ransomware
During the first half of this year, the number of incidents of ransomware has steadily increased. In early June, the security researchers at McAfee discovered “Tox,” which provides neophyte cybercriminals (aka script kiddies) with everything they need to run a ransomware campaign. We’ve seen this “malware-as-a-service” model before as spam, phishing, spyware, and virus packages are available for sale on the black market. The malware developers do this not only to monetize their work, but also to reduce their risk of being caught. With script kiddies getting involved, you can expect a continued increase in the number of ransomware attacks for the next several months as the hacker community tries to wring as much cash out of ransomware as possible.
As long as ransomware continues to generate cash for its purveyors, you can expect even more virulent strains of Cryptolocker and its variants to rear their ugly heads. Your goal is to make ransomware unprofitable by never having to pay the ransom. You can accomplish this by having a good off-site backup of your files, keeping your applications and operating system up to date, and remaining vigilant as you use your computer.
Sites consulted:
- Small Business Digest.
- The Guardian: www.theguardian.com/technology/2015/jun/02/ransomware-as-service-discovered-on-darknet.
- Reason Core Security.
- Hot for Security: http://www.hotforsecurity.com/blog/how-does-ransomware-work-the-ultimate-guide-to-understanding-ransomware-part-ii-11856.html.